Here is a subject I hear and get asked over and over again. Is Azure Active Directory (AAD) the same as Active Directory Domain Services (AD DS).
Let me be very clear. Azure Active Directory is NOT a cloud version of Active Directory Domain Services, and in fact, it bears minimal resemblance to its on-premises names at all.
The number one question I get asked: “How do I join my servers to Azure AD?”. IT admins expect (not unexpectedly) to be able to use Azure AD just like they have always used Active Directory Domain Services. So let’s compare AD DS (and particularly the domain services part of AD DS) to AAD. Let me educate you 🙂
What is Active Directory?
Most of us have probably worked with it for years, and now you’re looking to move to the cloud and understand what AAD is. Let’s start with a recap of what AD DS is.
Active Directory Domain Services was introduced as a hierarchical authentication and authorization database system to replace the flat file Domain system in use on NT4 and previous servers.
The NT4 domain model in 2000 was straining at the seams to keep up with evolving corporate structures, hampered by some quite severe limitations – maximum of 26,000 objects in a flat file “bucket”, only 5 kinds of fixed objects whose structure (properties etc.) could not be changed, maximum size of the database of 40Mb etc. NT4 Domains also primarily used NetBIOS (another flat file, Microsoft specific system) for its name resolution.
For a lot of larger organizations, this necessitated multiple domain databases with very limited and complicated interactions between those domains. Active Directory Domain Services (just called Active Directory in those days) was released with Windows Server 2000 and was based upon the X.500 hierarchical network standard that companies such as Novel’s NDS and Banyan Vines were using at the time.
AD DS also used DNS as its name resolution system and the TCP/IP communication protocols in use on the internet. It brought in the idea of a directory system which contained a “schema” database (the set of “rules” that define the properties or attributes of objects created in the “domain” database) which could be added to or “extended” to create either entirely new objects or new properties of existing objects.
Size limitations were also thrown out the window, with Microsoft creating directory systems in the billions of objects (given enough storage!) in their test labs.
Here is a list of the essential functions that make up AD DS:
- Secure Object store, including Users, Computers and Groups
- Object organization use OU’s, Domains and Forests
- Common Authentication and Authorization provider
- LDAP, NTLM, Kerberos
- Group Policy
- Customizable Schema
Along with Domain Services, there are also components like Certificate Services, Federation Services, and Privileged Access Management.
From its inception, AD DS quickly became the defacto directory system in most organizations, even today.
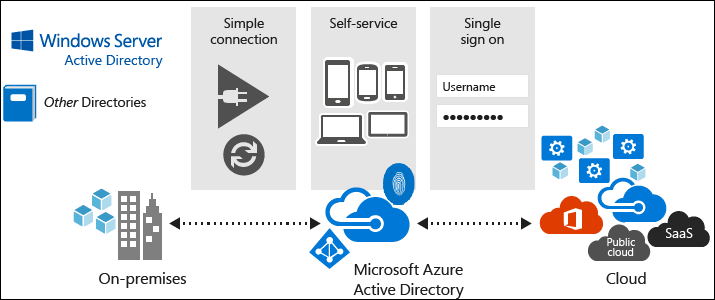
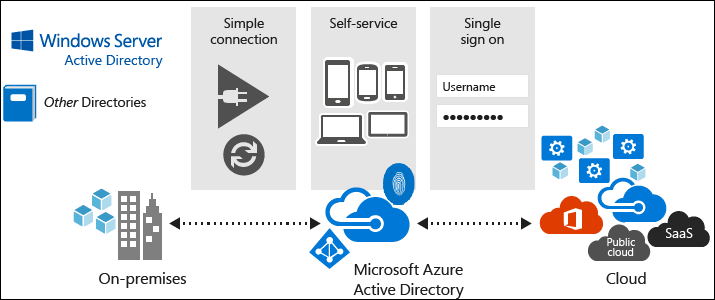
What is Azure Active Directory

So if you know what Active Directory Domain Services is, then how does this compare to Azure Active Directory? The answer to this is, not very closely. The decision to name AAD after AD, in my opinion, was more of a marketing decision than a technical one. This has lead to years of confusion. In many ways, AAD was designed for a world where PaaS and SaaS services were the default choice, not for IaaS in the cloud.
Azure Active Directory is a secure authentication store, which can contain users and groups, but that is about where the similarities end. AAD is a cloud-based identity management store for modern applications. AAD is designed to allow you to create users, groups, and applications that work with modern authentication mechanisms like SAML and OAuth.
Applications are an object that exists in AAD but not in AD DS. Applications allow you to create an identity for your applications that you can grant access for users to, and to allow you to grant your users access to applications owned by others.
What AAD does not provide is any AD DS service beyond user management.
- You can’t join computers to an Azure AD domain in the way you would with AD DS. There is something called Azure AD Join, but this is a different animal that I’ll address below. This means there are no computer objects in your AAD to apply things like GPOs to, and no centralized control of user rights on those machines.
- There is no Group Policy. AAD has some policy tools like conditional access, but it is more focused on access to applications.
- No support for LDAP, directory queries all use the REST API, Graph or PowerShell/CLI
- There’s no support for NTLM or Kerberos. AAD is modern authentication protocols only
- There’s no schema you have access to or can modify
- Flat structure, no OU’s, Domains or Forests
So, at this point, it’s obvious now that Azure AD is a very different thing to AD DS. AAD is for user, group and application management in the cloud. If your building all new services using PaaS or SaaS and using modern authentication protocols then you should be all set with AAD, it’s what it was designed for.
However, if your running IaaS in Azure and want AD DS to domain join machines and create GPO’s, then AAD won’t cut it for you (and that is by design).
Active Directory on Azure
Hopefully, now it’s clear what AAD is and isn’t, and if your building modern apps and AAD does what you need, then you can stop here.
However, if you are going down the IaaS route in Azure and you feel you still need the services of an AD domain, what alternatives are there?
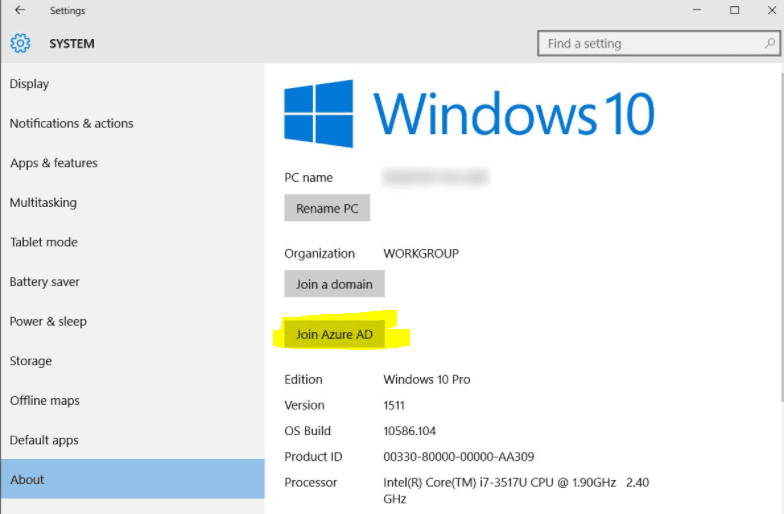
Azure AD Join
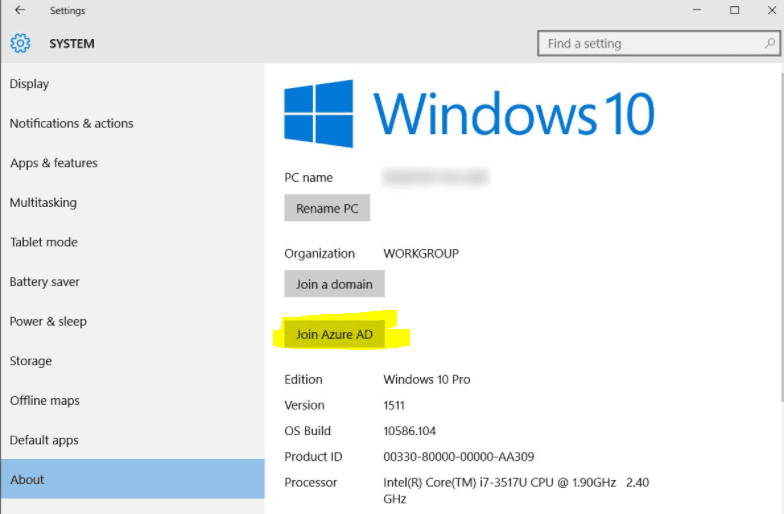
I mentioned this briefly earlier; it is possible to join devices directly to Azure AD. AAD Join is limited to Windows 10 machines only and provides limited functionality, certainly nothing like a full AD join.
When Azure AD joined, it is then possible to login to machines using Azure AD user accounts. You can apply conditional access policies that require machines to be AAD joined before accessing resources or applications. If you’re looking for a way to provide common user account management across Windows 10 machines, then this may work for you.
Azure AD Domain Services
If you need more than just user management, then it is possible to extend Azure AD to offer more AD based services using Azure AD Domain Services. AAD DS is an Azure product that you enable on your virtual network which deploys two domain controllers. They are managed by Microsoft and synchronized with your Azure AD tenant. This allows admins to grant machine access to users in your AAD tenant, but also to implement things like custom OU’s, group policy, LDAP queries, NTLM and Kerberos.
This is a domain managed by Microsoft, so you do not have to worry about patching your domain controllers or ensuring they are up. However, it also means you do not have full control of the domain. For example, you do not have domain admin rights, only enough rights to undertake the tasks Microsoft allows. You can see a full breakdown of AAD DS limitations here.
AD Domain Controllers on Azure
Nothing is stopping you just deploying some virtual machines in Azure and turning them into domain controllers. This is a support configuration and is in use by many people who need the full suite of services provided by AD inside Azure.
The downside to this approach is that you need to manage this yourself. You need to take care of patching and updating your servers, backing up your domain and any other maintenance you require. You are also in charge of making sure it is highly available and implementing a DR strategy if you require it. If you need all that AD DS has to offer then, this can be a great option, but if all you want is a common user store for machine login, it might be overkill.
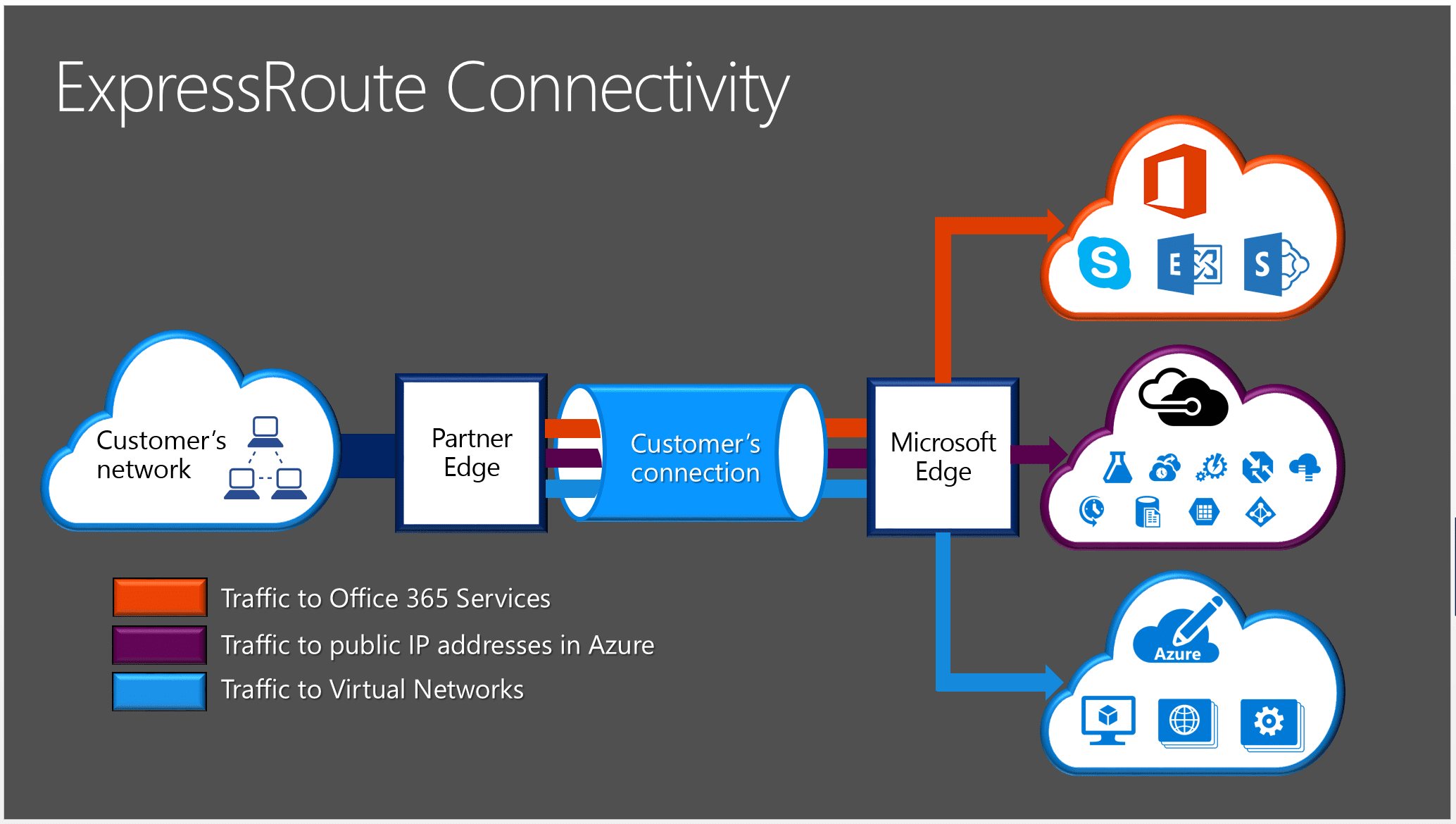
Access your On-Premises AD Domain
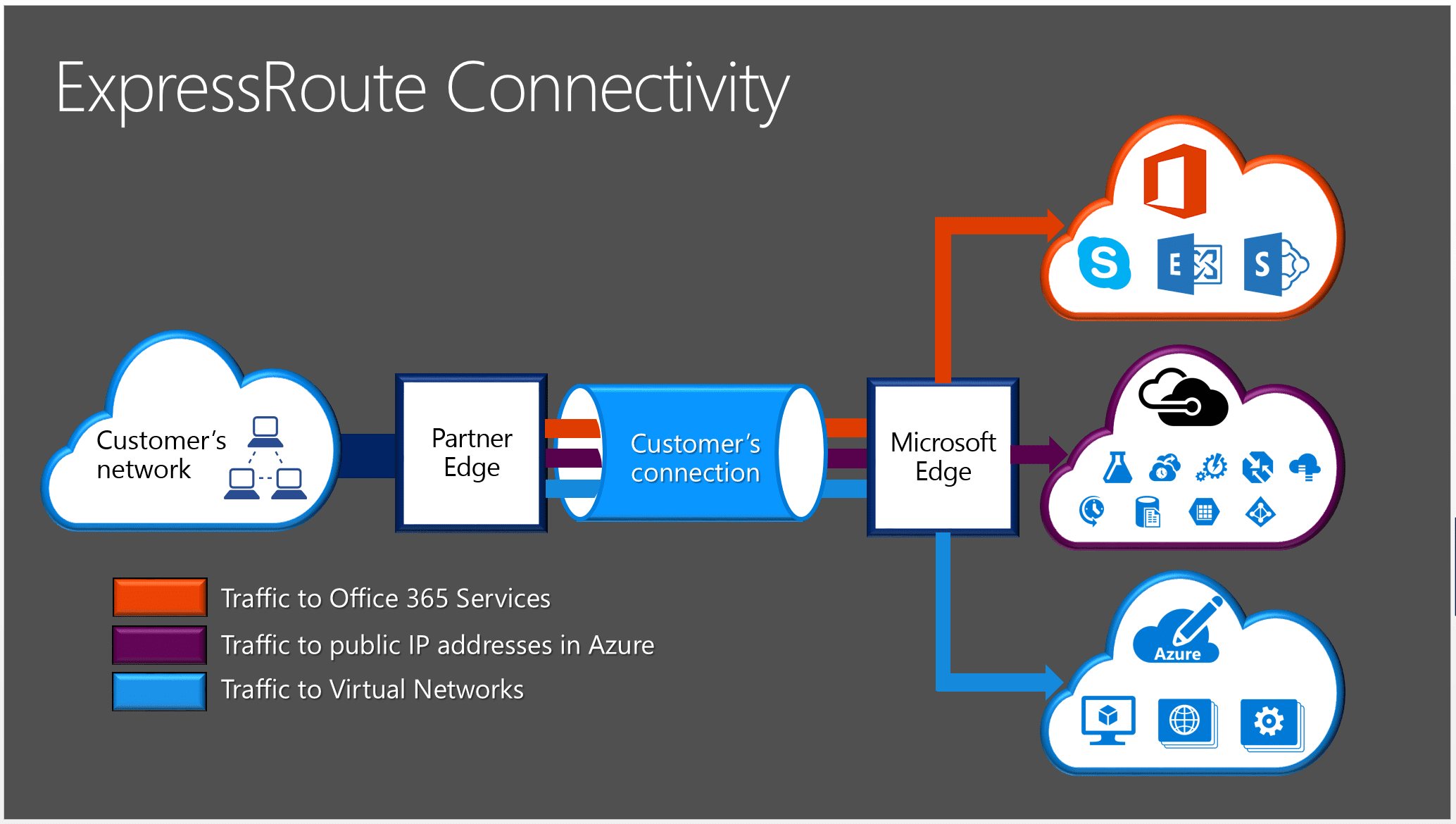
Finally, you can also extend your existing on-premises domain into Azure. Using ExpressRoute or VPN, you can connect your on-premises network to your Azure vNet and allow access to domain controllers. You can even deploy IaaS domain controllers in Azure that are joined to your on-premises domain. This then adds a dependency to your infrastructure of connectivity back to the on-premises network, so this connectivity becomes a key point of failure. You need to ensure that resiliency is built in.
Summary
If your new to Azure and especially identity in Azure, I hope clears things up. This is a new, modern authentication provider and is not Active Directory Domain Services in the cloud. AAD does not behave like the AD DS you know and love and really shouldn’t be compared to it, it is a different service.
If you need AD DS in your cloud environment, then there are options to achieve this, but AAD is not going to give you that. Take a look at the options listed in this blog post and see what meets your needs.
Until next time, Rob